My first post on “net neutrality” asked some questions. It appears here. Many people offered helpful thoughts and resources which have moved me along. This post is about trying to nail down some basics and extracting key findings from the FCC’s two rulings on “net neutrality”. A third post will follow which will define my position on the question before the legislature — state law to assure “net neutrality”. I’d really appreciate your further feedback at each stage.
Guiding Vision
Freedom of speech on the internet is a core value that we want to defend. The internet has enabled an explosion of communication, information sharing and business innovation that is of immense human value. The internet — revealed by search engines — has given us all much better access to information and has allowed many new voices to emerge and that is a good thing. We never want to go back to the last century in which information flow was much more restricted.
Rules for the Conversation
I’m going to try to follow several rules in thinking about this issue and ask that commenters do the same:
- Let’s not reason based on political affiliation. “Net neutrality” is something that Obama’s FCC embraced and Trump’s FCC has rejected. That gives me one good gut reason to like “net neutrality”, but I’m going to try to put that aside.
- Let’s not reason based on labels. “Net neutrality” absolutely sounds good, but we have to get beyond the packaging and make sure we understand the reality.
- Let’s not reason based on analogies and metaphors. Let’s not say things like “the internet is a highway” and without “net neutrality”, there will be “fast lanes and slow lanes.” The internet is not a highway, it does not have lanes and data packets are not cars. Nor is it a set of pipes or a public utility (although it has immense public value). When we say something is like something else, that is really an expression of how we feel about it, not an explanation.
- Let’s try not to oversimplify. This subject is maddeningly complicated and one wants to jump to a conclusion just so one can stop thinking about it.
Please call me on it when you think I’m not following these rules.
Basics: What is the internet?
To help avoid thought errors due to bad analogies, we have to try to bear in mind what the internet is. Here is a collection of basic concepts:
- Computers save data in files. Data in files can represent texts, data tables, images, sound recordings, video clips, etc.
- A computer network is a collection of computers linked so that they can share files and other resources. There are local area networks within homes and businesses. Some businesses with multiple locations have wide area networks. Links can be wired (copper or optical) or wireless.
- The internet is a collection of computers or computer networks communicating with each other across organizational ownership boundaries.
- There are billions of computers now communicating on the internet. Note that computers include not only desktops, laptops and smart phones, but all kinds of smaller devices — thermostats, smart watches, etc.
- Communication between computers requires that the computers follow established protocols. On the internet, these protocols have been established through an open, collaborative, international process involving both independent and business-affiliated engineers.
- On the internet, files are broken into standard sized packets of data, transmitted and reassembled at the receiving destination.
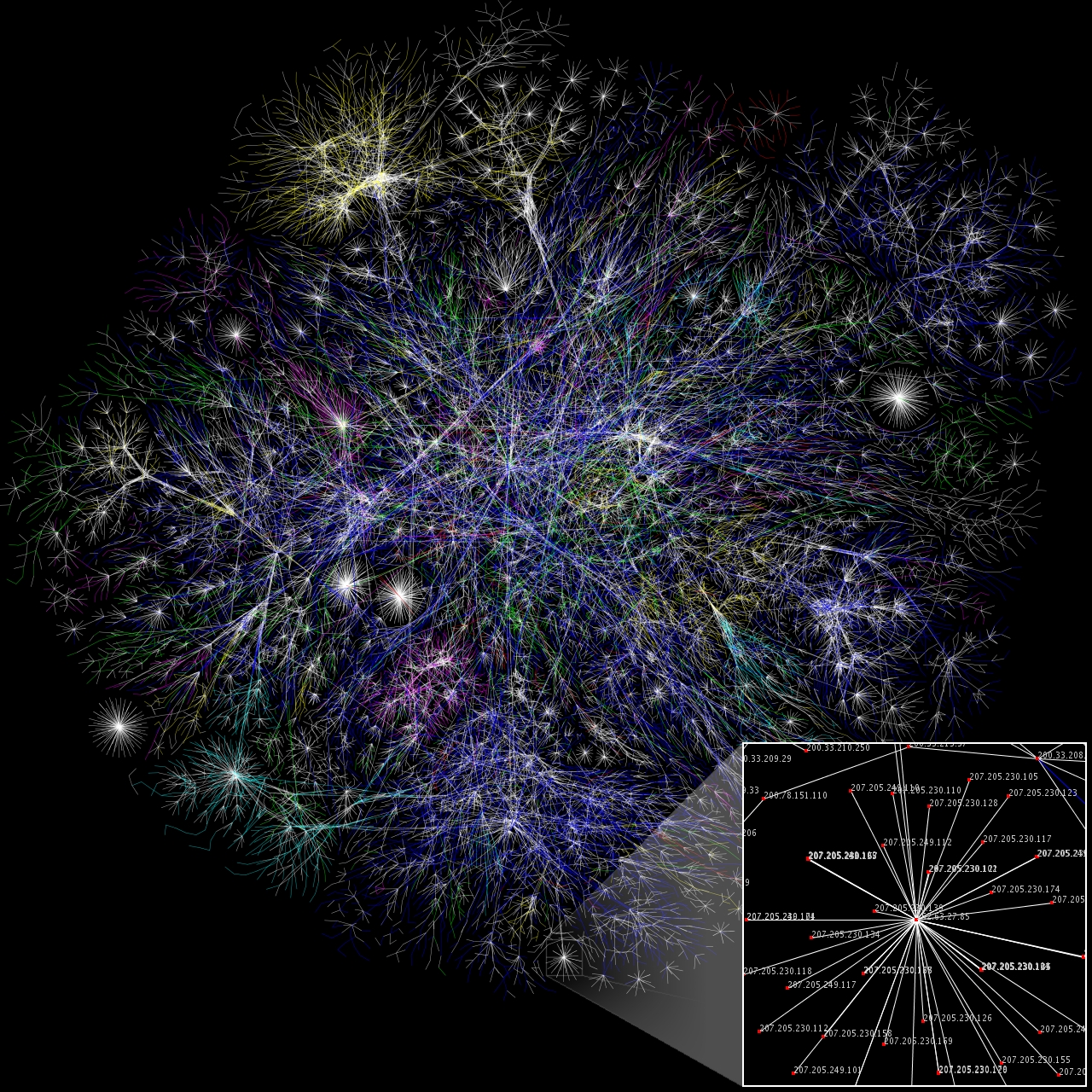
- Data packets are not sent directly from origin to destination. Instead data packets are routed through connected nodes — computers that route data. The image above displays the internet topology of connected nodes. See also this actual map of the major nodes. You can see the node hops that packets take from any website to your home computer by running a traceroute. For example, from my home computer to willbrownsberger.com, data packets go through the following nodes (each one of which is actually not just one computer, but a network of computers):
1 wireless_broadband_router [the router in my office owned by me]
2 lo0-100.bstnma-vfttp-326.verizon-gni.net (71.248.161.1) [Verizon]
3 b3326.bstnma-lcr-22.verizon-gni.net (100.41.136.68) [Verizon]
4 * * * [node won’t self identify]
5 * * * [node won’t self identify]
6 0.ae5.br1.nyc1.alter.net (140.222.228.107) [ AlterNet acquired by Verizon]
7 ae13.cr0-nyc2.ip4.gtt.net (173.205.47.145) [GTT, international internet company]
8 xe-8-2-2.cr0-nyc4.ip4.gtt.net (89.149.181.190) [GTT, international internet company]
9 cloudflare-gw.cr0-nyc4.ip4.gtt.net (69.174.23.54) [Cloudflare server housed at GTT]
10 104.25.146.119 (104.25.146.119) [Cloudflare server] - The Internet Protocol governs the routing of packets from node to node. Your home modem has an IP address. Each website has an IP address. IP addresses are unique numbers defined by international convention. Each packet that a node receives includes the IP address which defines its ultimate destination. The routing of packets across nodes can vary according to congestion or network outages and depends on nodes maintaining information about the status and connection structure of the network. Routing is complicated!
- Communications protocols are conceptualized in layers. The link layer protocol governs the communications between two connected computers. One service provided by the link layer is flow control, throttling so that a fast sender does not overwhelm a slower receiver. Flow control is also provided by the transport layer which runs on the origin and destination computers.
Who owns the internet?
No one. It is not a public utility that is governed by a single board, but rather a collaborative project among multiple kinds of entities that has taken 50 years to evolve. Here are the kinds of entities comprising the internet, arrayed in order that a packet might traverse from you to this website:
- Connected device: The desktop or lap top or cell phone that you own or rent.
- Perhaps a local router: If you are at home, this probably sits on your desk and has the label of your ISP on it.
- Internet Service Provider (ISP): The company which connects directly to your device or home router. ISPs connecting to homes in Massachusetts include Verizon, Comcast and RCN. Cell phone providers also function as ISPs. In the old days, you would connect to your ISP over your phone line and the ISP would connect you on to the internet. Over the past couple of decades, the ISP market has consolidated dramatically as phone and cable companies have started offering broadband Internet Access Services (BIAS) and have become ISPs. ISP/BIAS consolidation has progressed further due to cable company consolidation and wireless provider consolidation. Nationwide in 2013, 6 companies had almost three quarters of the ISP market and consolidation continues.
- Backbone: The companies that own nodes and connections that route packets of data to and from ISPs. These can be referred to as Internet Backbone Providers, IBPs. Any traveling packet might cross nodes owned by multiple IBPs. I have annotated the traceroute output above to show that packets going from my home to my website run through several different Verizon nodes, a couple of unidentified nodes and a couple of GTT nodes before reaching Cloudflare. The connections between IBPs are governed by interconnection agreements. These agreements can take different forms. Some of the agreements are settlement free — no money is exchanged and both networks make money from their own customers (which would mostly be ISPs) and benefit from the interconnection. In others, one network pays the other for access or transit privileges.
- ISP or CDN:
- ISP: A website needs an ISP to connect to Internet Backbone Provider. A website could have essentially the same relationship to the internet that you do — it buys access through an ISP.
- Content Delivery Network: Alternatively, many websites now connect to end users via a content delivery network. A CDN distributes copies of frequently accessed website pages or page components to multiple servers located within IBP data centers or even directly within ISP data centers. That means that data packets composing a webpage go through fewer hops to get to the end user. A CDN offers security and reliability benefits as well as speed. My website uses Cloudflare CDN. The CDN needs to have an agreement with the IBP or ISP and likely pays them. Some major content providers like Google have their own CDN.
- Hosting company or corporate server: Ultimately, there is a computer someplace that stores/creates the primary image of a web page or other kind of content (e.g., video). That could even be a home computer, but most likely it is a corporate data center or a hosting company. A hosting company has racks of computers that it rents to smaller websites like this one and typically has its own relationship with one or more ISPs. My website runs at InmotionHosting.
All citations below to the FCC’s net neutrality 2015 ruling, are in the following form: FCC2015-xx where xx is the paragraph number. Citations to the the FCC’s 2017 ruling reversing the 2015 ruling are in the following form: FCC2017-xx.
Regulating the Internet — the 2015 FCC Ruling
So, what did the FCC’s 2015 net neutrality ruling actually do? First, the FCC created some bright line rules applicable to broadband ISPs in their role connecting with consumers:
- No blocking: . . . A person engaged in the provision of broadband Internet access service, insofar as such person is so engaged, shall not block lawful content, applications, services, [in other words, any lawful traffic] or non-harmful devices, subject to reasonable network management.
- No throttling: . . . A person engaged in the provision of broadband Internet access service, insofar as such person is so engaged, shall not impair or degrade lawful Internet traffic on the basis of Internet content, application, or service, or use of a non-harmful device, subject to reasonable network management.
- No paid prioritization: . . . A person engaged in the provision of broadband Internet access service, insofar as such person is so engaged shall not engage in paid prioritization. “Paid prioritization” refers to the management of a broadband provider’s network to directly or indirectly favor some traffic over other traffic, including through use of techniques such as traffic shaping, prioritization, resource reservation, or other forms of preferential traffic management, either (a) in exchange for consideration (monetary or otherwise) from a third party, or (b) to benefit an affiliated entity. . . . The Commission may waive the ban on paid prioritization only if the petitioner demonstrates that the practice would provide some significant public interest benefit and would not harm the open nature of the Internet.
FCC2015-15-18 (emphasis added). In addition to these bright line rules, it added a general statement that:
Any person engaged in the provision of broadband Internet access service, insofar as such person is so engaged, shall not unreasonably interfere with or unreasonably disadvantage (i) end users’ ability to select, access, and use broadband Internet access service or the lawful Internet content, applications, services, or devices of their choice, or (ii) edge providers’ ability to make lawful content, applications, services, or devices available to end users. Reasonable network management shall not be considered a violation of this rule.
FCC2015-21 (emphasis added). Finally, the Commission continued in effect a transparency principle essentially to cover the notable loophole for “network management” that appears in the blocking, throttling and reasonability rules:
A person engaged in the provision of broadband Internet access service shall publicly disclose accurate information regarding the network management practices, performance, and commercial terms of its broadband Internet access services sufficient for consumers to make informed choices regarding use of such services and for content, application, service, and device providers to develop, market, and maintain Internet offerings.
FCC2015-23. The ruling was limited in scope to the Broadband Internet Access Service Providers, both mobile and fixed, as they face consumers. It defined BIAS as:
A mass-market retail service by wire or radio that provides the capability to transmit data to and receive data from all or substantially all Internet endpoints, including any capabilities that are incidental to and enable the operation of the communications service, but excluding dial-up Internet access service. This term also encompasses any service that the Commission finds to be providing a functional equivalent of the service described in the previous sentence, or that is used to evade the protections set forth in this Part.
FCC2015-25.
The 2015 rules do not apply to the internet backbone providers (IBPs) or to content delivery networks (CDNs) that bypass the IBPs. The 2015 rules reaffirm the FCCs conclusion in 2000 that it should not regulate the internet backbone — that competition among IBPs, moderated by antitrust laws, would suffice to preserve an open access to the backbone for ISPs and their customers. It is worth noting that physical telecommunications lines may be owned separately from the IBPs transmitting data over those lines. The physical telecommunications lines themselves also carry voice and other signals and are regulated as common carriers.
Further, the ruling does not govern the interconnection agreements between the BIAS/ISPs and (i) the IBPs; (ii) the CDNs; or (iii) huge content providers like Google and Netflix that may connect directly to the BIAS/ISPs. While the ruling asserts jurisdiction over these interconnections and the authority to hear disputes, it does not put in place rules. Essentially, the FCC acknowledges that interconnection practices are changing too fast to understand or regulate at this time. FCC2015-30. More on this further below.
As to the “network management” exceptions in the rules, the FCC attempts to draw a distinction between technical and business decisions
A network management practice is a practice that has a primarily technical network management justification, but does not include other business practices. A network management practice is reasonable if it is primarily used for and tailored to achieving a legitimate network management purpose, taking into account the particular network architecture and technology of the broadband Internet access service.
FCC2015-32. Especially in the mobile context, where capacity is still scarce, there are some gray areas. Is it a technical decision or a business decision if Verizon throttles super-heavy video users? On the one hand, it is failing to provide the users the unlimited capacity it promised, but on the other hand it is protecting other users from degraded service.
The legal foundation for the FCC’s new rules is a classification of BIAS/ISPs as common carriers subject to Title II of the Telecommunications Act of 1934. So reclassifying the BIAS/ISPs gives the FCC authority to apply a host of regulations, extending even to pricing. However, in the 2015 ruling, the FCC exerted “forbearance” and introduced only the relatively limited “net neutrality” rules, relying on sections 201, 202 and 208 of Title II. Additionally, the FCC applies rules related to privacy, disabilities access and infrastructure access.
The Broadband market as the 2015 FTC understood it
The fundamental motivation of the 2015 FCC’s net neutrality ruling was the perceived power of broadband providers:
[B]roadband providers are in a position to act as a “gatekeeper ” between end users’ access to edge providers’ applications, services, and devices and reciprocally for edge [content and service] providers’ access to end users. Broadband providers can exploit this role by acting in ways that may harm the open Internet , such as preferring their own or affiliated content, demanding fees from edge providers, or placing technical barriers to reaching end users.
. . . The broadband provider’s position as gatekeeper is strengthened by the high switching costs consumers face when seeking a new service. Among the costs that consumers may experience are: high upfront device installation fees; long-term contracts and early termination fees; the activation fee when changing service providers; and compatibility costs of owned equipment not working with the new service.
. . . [C]onsumers are unsure about the causes of problems or limitations with their services — for example, whether a slow speed on an application is caused by the broadband provider or the edge provider — and as such consumers may not feel that switching providers will resolve their Internet access issues.
FCC2015-80-81. Broadband providers have the technical ability to preference traffic from particular sources. FCC2015-85. We should assume that they will use that power to their commercial benefit. They are most likely to disadvantage traffic that directly competes with services that they provide themselves. For example, cable providers who also produce and distribute content have incentives to throttle Netflix. Mobile providers have incentive to block internet calling services like Skype and Facetime. FCC2015-96.
The Backbone market and interconnections as the 2015 FTC understood them
As noted above, while requiring neutrality on the last mile, the FCC chose not to require neutrality the connections between the broadband providers and the backbone, making the following observations about the state of the market.
Internet traffic exchange is typically based on commercial negotiations. Changes in consumer behavior, traffic volume, and traffic composition have resulted in new business models for interconnection. Since broadband Internet access service providers cannot, on their own, connect to every end point on the Internet in order to provide full Internet access to their customers, they historically paid third-party backbone service providers for transit. Backbone service providers interconnected upstream until traffic reached Tier 1 backbone service providers, which peered with each other and thereby provided their customer networks with access to the full Internet. In this hierarchical arrangement of networks, broadband Internet access providers negotiated with backbone service providers; broadband Internet access providers generally did not negotiate with edge providers to gain access to content. However, in recent years, new business models of Internet traffic exchange have emerged, premised on changes in traffic flows and in broadband Internet access provider networks. A number of factors drive these trends in Internet traffic exchange.
Critically, the growth of online streaming video services has sparked further evolution of the Internet. Content providers have come to rely on the services of commercial and private CDNs, which cache content close to end users, providing increased quality of service and avoiding transit costs. While CDNs rely on transit to feed the array of CDN cache servers, they deliver traffic to broadband Internet access service providers via transit service or by entering into peering arrangements, directly interconnecting with broadband Internet access service providers.
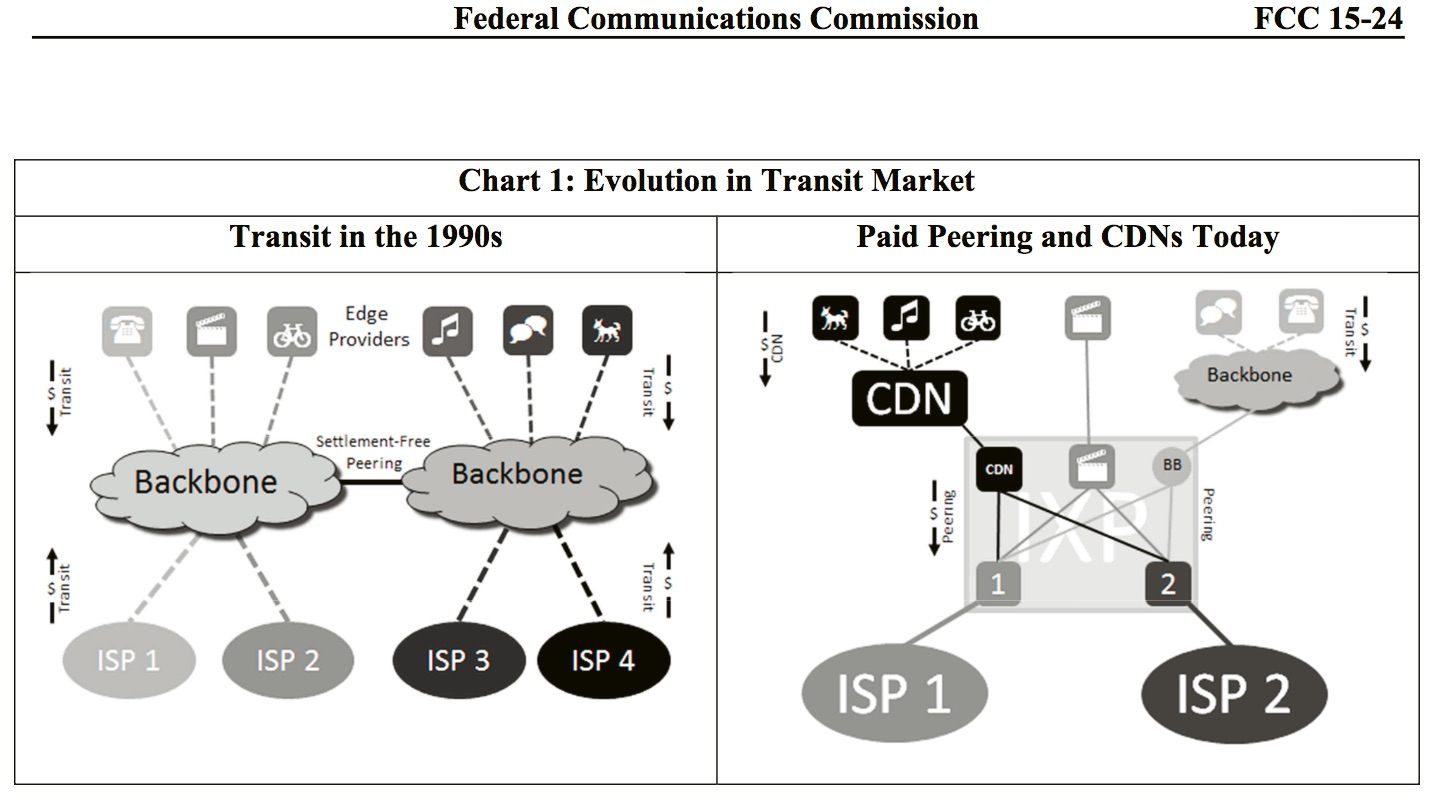
In addition, several large broadband Internet access service providers, such as AT& T, Comcast, Time Warner Cable, and Verizon, have built or purchased their own backbones, giving them the ability to directly interconnect with other networks and edge providers and thereby lowering and eliminating payments to third-party transit providers . These interconnection arrangements are “peering,” involving the exchange of traffic only between the two networks and their customers, rather than paid transit, which provides access to the full Internet over a single interconnection. Peering gives the participants greater control over their traffic and any issues arising with the traffic exchange are limited to those parties, and not other parties over other interconnection links. Historically, broadband Internet access service providers paid for transit and therefore had an incentive to agree to settlement-free peering with a CDN to reduce transit costs; however, where large broadband Internet access service providers have their own national backbones and have settlement-free peering with other backbones, they may no longer have an incentive to agree to settlement-free peering with CDNs in order to avoid transit costs. As shown below in Chart 1, the evolution from reliance on transit to peering arrangements also means an evolution from a traffic exchange arrangement that provides access to the full Internet to a traffic exchange arrangement that only provides for the exchange of traffic from a specific network provider and its customers.
The Heart of the Question — Paying for Video Infrastructure, FCC’s ambivalence in 2015.
Computer files vary widely in size. For example, the files comprising the web page you are reading add up to 2 million bytes of data. Most of that is in the two images that the page contains. The 80 second video at the top of the page derives from a 120 million byte mp4 file. A typical page on this website without images might only add up to a couple hundred thousand characters of data. By contrast, if, instead of reading a typical page on this site for three minutes, you watched a three minute Youtube video (at a lower quality 30 frames per second), you would download approximately 200 million characters of digitized video, roughly 1000-fold as much data.
Prior to the availability of high-speed “broadband” connections to the home, it was physically impossible to stream video, but streaming video now dominates the internet. Five years ago, in 2013, Netflix and Youtube alone already accounted for 50% of the peak download traffic in the internet. FCC2015-197 (fn 490). In 2016, Netflix alone was 35% of the traffic on fixed broadband lines and all video accounted for 73% of internet traffic.
That rapid transition to video is what has generated most of the controversy over the past few years. Huge video providers, basically Google/Youtube and Netflix, are generating gobs of additional traffic that the BIAS/ISPs can’t handle without upgrading their networks. Who should pay for that? Should the broadband providers charge all their customers more to pay for more infrastructure so that some customers can watch Netflix without any stutters? Or should Netflix pay for access to the ISP and impose the costs on its own subscribers? And while the dispute is unresolved, should the ISP allow Netflix traffic to degrade traffic going to customers who don’t use video or should it throttle Netflix traffic to protect its network? And, by the way, do customers who are not using video even notice the degradation? Variable slight delays in a page loading in a web browser are routine — slight delays are much more annoying to video users than to other users.
FCC2015-201. Translation: No, actually the cost of handling all this video traffic is really significant and it isn’t just about the last mile connection. We need a lot of new infrastructure and it isn’t fair for all of our customers who don’t user Netflix to fund that. The old idea that connections between networks should be free assumed a two-way street. Netflix is drowning us in traffic and giving us nothing in return.
That narrative also has a ring of truth to it, given the explosive growth of video. One persuasive counter argument (offered by an acquaintance engineer) is that adding new internet-facing port capacity is vastly less expensive than adding new broadband last-mile capacity. If the last-mile is not actually congested, then the refusal to add more port capacity may be simple commercial extortion.
In the end, the 2015 FCC punted, choosing not to apply neutrality rules in these agreements, but asserted its jurisdiction to regulate them on a case-by-case basis and learn from the experience.
Given the constantly evolving market for Internet traffic exchange, we conclude that at this time it would be difficult to predict what new arrangements will arise to serve consumers’ and edge providers’ needs going forward, as usage patterns, content offerings, and capacity requirements continue to evolve. Thus, we will rely on the regulatory backstop prohibiting common carriers from engaging in unjust and unreasonable practices.
FCC2015-203. This is not an insignificant statement — it is an assertion of authority to resolve disputes. But it stops well short of enforcing net neutrality.
Further weakening any rigid principle of neutrality is the “network management” exception, allowing blocking or throttling in the last mile.
We recognize the need to ensure that the reasonable network management exception will not be used to circumvent the open Internet rules while still allowing broadband providers flexibility to experiment and innovate as they reasonably manage their networks. We therefore elect to maintain a case-by-case approach.
FCC2015-218. Is it a reasonable network practice to throttle an overwhelming burst of traffic coming from one provider like Netflix that creates congestion that has the effect of degrading service to the millions of little websites like this one on the internet? That remains to be seen, but the FCC does warn that:
[N]etwork management practices that alleviate congestion without regard to the source, destination, content, application, or service are also more likely to be considered reasonable network management practices in the context of this exception.
FCC2015-220.
Summary of the FCC’s 2015 Position
By explicitly prohibiting throttling, blocking and and paid prioritization of content on the last mile connection offered by broadband providers, the FCC spoke directly to civil libertarian fears that the broadband providers might block free speech and shut out new voices among the currently estimated over 100 million active websites in the world.
That much is a step forward, but it probably makes little practical difference. Broadband providers have some commercial incentive to generally provide what people want and believe they are paying for: Access broadly to the content of the internet. The idea of curated content died in the 90s with AOL. No one company can compete with the spectacular diversity of content available on the raw internet. Moreover, the day they start refereeing content is the day they start to risk liability for fraudulent or offensive content, which they certainly want to avoid. And the Federal Trade Commission previously had power to bring enforcement actions against them for failing to provided promised access — see further discussion below under the 2017 ruling.
On the much more real and difficult issue of how to handle the rise of radically voluminous video content, the FCC basically punted by declining to require neutrality on the interconnections to broadband providers. Broadband providers can drag their feet on adding capacity to an existing peering port until content providers or their intermediaries (other ISPs, CDNs, or IBPs) agree to pay up for a faster open port.
Let us assume, for the sake of argument, that ISPs do drag their feet and extort video providers into buying access to a dedicated port. Is this harmful to consumers or other providers? Perhaps not so much. First, the video providers that caused the congestion on the original port eventually move off that port and relieve congestion. If Netflix is a third of internet traffic, its movement to a dedicated port benefits everyone else greatly. Second, while congestion lasts during a commercial dispute, the only users likely to be significantly disadvantaged are the video users contributing to the problem. As noted above, most other web experiences do not suffer greatly from millisecond delays.
Nor are “new voices” on the internet stifled in this congestion scenario. Most new voices are not going to create their own video publishing platform. They will avail themselves of Youtube or Facebook and publish away through the high capacity content delivery networks that these companies have paid to build. Granted, an upstart successor to Youtube faces barriers to entry, but ISP traffic tolls is not the largest of them.
These considerations may have been in the minds of some of the decision-makers in Obama’s FTC as it decided not to go whole-hog on commercial net neutrality, but to take a more limited and symbolic step.
FCC’s 2015 Comments on State Regulation
The Obama FCC did assert strong pre-emption of state-regulation.
Today, we reaffirm the Commission’s longstanding conclusion that broadband Internet access service is jurisdictionally interstate for regulatory purposes. As a general matter, mixed jurisdiction services are typically subject to dual federal/state jurisdiction, except where it is impossible or impractical to separate the service’s intrastate from interstate components and the state regulation of the intrastate component interferes with valid federal rules or policies. With respect to broadband Internet access services, the Commission has previously found that, “[a]lthough . . . broadband Internet access service traffic may include an intrastate component, . . . broadband Internet access service is properly considered jurisdictionally interstate for regulatory purposes.” The Commission thus has evaluated possible state regulations of broadband Internet access service to guard against any conflict with federal law. Though we adopt some changes to the legal framework regulating broadband, the Commission has consistently applied this jurisdictional conclusion to broadband Internet access services, and we see no basis in the record to deviate from this established precedent. The “Internet’s inherently global and open architecture” enables edge providers to serve content through a multitude of distributed origination points, making end -to-end jurisdictional analysis extremely difficult —if not impossible —when the services at issue involve the Internet.
We also make clear that the states are bound by our forbearance decisions today. Under section 10(e), “[a] State commission may not continue to apply or enforce any provision” from which the Commission has granted forbearance. With respect to universal service, we conclude that the imposition of state-level contributions on broadband providers that do not presently contribute would be inconsistent with our decision at the present time to for bear from mandatory federal USF contributions, and therefore we preempt any state from imposing any new state USF contributions on broadband —at least until the Commission rules on whether to provide for such contributions. We recognize that section 254 expressly contemplates that states will take action to preserve and advance universal service, but as discussed below, our actions in this regard will benefit from further deliberation.
Finally, we announce our firm intention to exercise our preemption aut1ority to preclude states from imposing obligations on broadband service that are inconsistent with the carefully tailored regulatory scheme we adopt in this Order. While we establish a comprehensive regulatory framework governing broadband Internet access services nationwide today, situations may nonetheless arise where federal and state actions regarding broadband conflict. The Commission has used preemption to protect federal interests when a state regulation conflicts with federal rules or policies, and we intend to exercise this authority to preempt any state regulations which conflict with this comprehensive regulatory scheme or other federal law. For example, should a state elect to restrict entry into the broadband market through certification requirements or regulate the rates of broadband Internet access service through tariffs or otherwise, we expect that we would preempt such state regulations as in conflict with our regulations. While we necessarily proceed on a case-by-case basis in light of the fact specific nature of particular preemption inquiries, we will act promptly, whenever necessary, to prevent state regulations that would conflict with the federal regulatory framework or otherwise frustrate federal broadband policies.
FCC2015-431-3.
The FCC’s 2017 Ruling
In December 2017, the FCC reversed the 2015 ruling. It issued a new declaratory ruling, finding that Broadband Internet Access Services should not, after all, be classified as telecommunications services, but as “information services”. This means that they are not common carriers of which the FCC can require neutrality.
In finding that broadband services are not common carriers, the 2017 FCC makes different statutory construction arguments for fixed and mobile broadband. First, it argues that fixed broadband is not just a common telecommunications carrier service — it includes various data services that are inextricably bound with internet access such as domain name lookup and caching and it should be classified as an information service. Second, the 2017 FCC found that wireless broadband is not a common carrier telecommunications service because it does not meet the definition of commercial mobile service (which would require that it use the phone numbering system for communication).
Going beyond the statutory arguments, the 2017 FCC finds that investment in broadband capacity dropped after the 2015 FCC order. This finding requires choosing among alternative accounting methods for investment. FCC2017-91ff. In general, the 2017 FCC takes a dim view of the consequences of regulation:
Utility-style regulation is particularly inapt for a dynamic industry built on technological development and disruption. It is well known that extensive regulation distorts production as well as consumption choices. Regulated entities are inherently restricted in the activities in which they may engage, and the products that they may offer. Asking permission to engage in new activities or offer new products or services quickly becomes a major preoccupation of the utility. Within the communications industry, it is apparent that the most regulated sectors, such as basic telephone service, have experienced the least innovation, whereas those sectors that have been traditionally free to innovate, such as Internet service, have greatly evolved. In the communications industry, incumbents have often used Commission regulation under the direction of the “public interest” to thwart innovation and competitive entry into the sector and protect existing market structures. Given the unknown needs of the networks of the future, it is our determination that the utility-style regulations potentially imposed by Title II run contrary to the public interest.
The record confirms that concern about “regulatory creep”—whereby a regulator slowly increases its reach and the scope of its regulations—has exacerbated the regulatory uncertainty created by the Title II Order. Even at the time of adoption, the Commission itself did not seem to know how the Title II Order would be interpreted. As then-Chairman Wheeler stated in February 2015, “we don’t really know. No blocking, no throttling, no fast lanes. Those can be bright-line rules because we know about those issues. But we don’t know where things go next.” With future regulations open to such uncertainties, Title II regulation adds a risk premium on each investment decision, which reduces the expected profitability of potential investments and deters investment. For example, the Title II Order did not forbear from ex post enforcement actions related to subscriber charges, raising concerns that ex post price regulation was very much a possibility. Further, providers have asserted that although the Commission forbore from the full weight of Title II in the Title II Order, they were less willing to invest due to concerns that the Commission could reverse course in the future and impose a variety of costly regulations on the broadband industry—such as rate regulation and unbundling/open access requirements—placing any present investments in broadband infrastructure at risk. These concerns were compounded by the fact that while the Title II Order itself announced forbearance from ex ante price regulation, at the same time it imposed price regulation with its ban on paid prioritization arrangements, which mandated that ISPs charge edge providers a zero price. These threats to the ISP business model have been felt throughout financial markets. As Craig Moffett of MoffettNathanson explained, “[i]t would be naïve to suggest that the implication of Title II, particularly when viewed in the context of the FCC’s repeated findings that the broadband market is non-competitive, doesn’t introduce a real risk of price regulation.” These risks are not merely theoretical: As CenturyLink contends, financial analysts lowered industry stock ratings due in part to the major risks Title II posed to the industry, which resulted in lower stock prices and lost market capitalization.
FCC2017-100-1. As to the large commercial video disputes, it is certainly true that the FCC’s earlier ruling offered little guidance, but did raise the possibility of intervention.
Conversely, the 2017 FCC argues that the examples of discrimination that 2015 FCC sought to prevent were not evidence of a general risk of content discrimination.
The Internet thrived for decades under the light-touch regulatory regime in place before the Title II Order, as ISPs built networks and edge services were born. We find that the sparse evidence of harms discussed in the Title II Order—evidence repeated by commenters in this proceeding as the basis for adopting a Title II classification—demonstrates that the incremental benefits of Title II over light-touch regulation are inconsequential, and pale in comparison to the significant costs of public-utility regulation.
The Internet as we know it developed and flourished under light-touch regulation. It is self-evident that the hypothetical harms against which the Title II Order purported to protect did not thwart the development of the Internet ecosystem. Edge providers have been able to disrupt a multitude of markets—finance, transportation, education, music, video distribution, social media, health and fitness, and many more—through innovation, all without subjecting the networks that carried them to onerous utility regulation. It is telling that the Title II Order and its proponents in this proceeding can point only to a handful of incidents that purportedly affected Internet openness, while ignoring the two decades of flourishing innovation that preceded the Title II Order.
FCC2017-109-110. They review the misconduct instances noted in the 2015 order and find that they were exceptions that proved the rule that the internet access has generally been neutral without regulation. All but one of a collection of examples of abuse from the Free Press all have to do with competing services or congestion issues.
Finally, the 2017 FCC argues that the other business and regulatory incentives that broadband internet providers face compel their openness.
The content and applications produced by edge providers often complement the broadband Internet access service sold by ISPs, and ISPs themselves recognize that their businesses depend on their customers’ demand for edge content. It is therefore no surprise that many ISPs have committed to refrain from blocking or throttling lawful Internet conduct notwithstanding any Title II regulation. Finally, to the extent these economic forces fail in any particular situation, existing consumer protection and antitrust laws additionally protect consumers.
FCC2017-117. Even the head of Netflix apparently agrees that the consumer demand for neutrality is sufficiently compelling to control ISP behavior without regulation.
The 2017 FCC disputes the argument that broadband services are monopoly providers with huge market power, including this table which shows that most people live in areas with more than one high speed provider:
| Percent of U.S. population in developed census blocks in which residential broadband wireline ISPs reported deployment (as of December 31, 2016)[1] | ||||
| Number of providers | ||||
| Speed of at least: | 3+ | 2 | 1 | 0 |
| 3 Mbps down and 0.768 Mbps up | 12.1% | 67.2% | 16.2% | 4.4% |
| 10 Mbps down and 1 Mbps up | 9.0% | 58.5% | 26.3% | 6.2% |
| 25 Mbps down and 3 Mbps up | 5.9% | 45.2% | 39.6% | 9.2% |
So, 79.3% have at least two services available at 3Mbps down speed. If satellite and terrestrial wireless (not mobile wireless) are included, the share with some 2 or more options goes up to 99.8%. They make the point that since most of the costs are fixed, it only takes two providers to create strong competition for customers. They also make the point that mobile providers offer competition to land line providers. FCC2017-124-6
In terms of raw financial power, the 2017 FCC makes this point:
[L]arger edge providers, such as Amazon, Facebook, Google and Microsoft, likely have significant advantages that would reduce the prospect of inefficient outcomes due to ISP market power. For example, the market capitalization of the smallest of these five companies, Amazon, is more than twice that of the largest ISP, Comcast, and the market capitalization of Google alone is greater than every cable company in America combined.
FCC2017-134. And to the extent we are concerned about protecting new competitors to these established content players, the ISPs may actually have incentives to favor them, both to increase the value of their own services and to reduce the dominance of the established content players. FCC2017-133.
The FCC emphasizes that these reclassifications do not deregulate broadband. Instead, they shift the regulatory authority from the FCC to the FTC. Although the reclassification reduces the power of the Federal Communications Commission to regulate, it increases the power of the Federal Trade Commission to regulate. While the FCC has power over common telecommunications carriers, the FTC is specifically barred from regulating them.
So, for example, while ATT mobile broadband would prefer not to be classified a common carrier for neutrality purposes, it made more or less the opposite argument in recent FTC regulatory case about throttling. ATT argued that since ATT was in some roles (long distance backbone telecom) a common carrier, it was a common carrier for all purposes, so that while providing mobile broadband it was a common carrier exempt from FTC regulation. A high federal appeals court recently disagreed, finding that FTC jurisdiction depends on whether or not as to a particular activity ATT is acting as a common carrier. Since mobile broadband is not a common carrier activity under pre-2015 law and post-2017 law, the FTC can regulate. This finding allows the FTC to regulate ATT’s throttling of service to heavy smart phone users. However, the FTC’s regulatory approach is reactive enforcement as opposed to rulemaking.
So, the very same fundamental struggle between video providers who create huge network loads and broadband providers who have finite network capacity will continue to be refereed by a regulator. From a user perspective, there are powerful arguments to be made in front of the FTC — a broadband provider that promises to provide general internet access at a certain speed and doesn’t is engaging in deceptive trade practices. FCC2017-141. For a state level example of fair trade enforcement, see New York’s case against Time Warner.
Additionally, a broadband provider that leveraged market power unfairly could be in violation of antitrust laws.
The case-by-case, content-specific analysis established by the rule of reason will allow new innovative business arrangements to emerge as part of the ever-evolving Internet ecosystem. New arrangements that harm consumers and weaken competition will run afoul of the Sherman Act, and successful plaintiffs will receive treble damages. The FTC and DOJ can also bring enforcement actions in situations where private plaintiffs are unable or unwilling to do so. New arrangements benefiting consumers, like so many Internet innovations over the last generation, will be allowed to continue, as was the case before the imposition of Title II utility-style regulation of ISPs.
FCC2017-148.
The 2017 FCC preserves an apparently strong transparency rule:
Any person providing broadband Internet access service shall publicly disclose accurate information regarding the network management practices, performance, and commercial terms of its broadband Internet access services sufficient to enable consumers to make informed choices regarding the purchase and use of such services and entrepreneurs and other small businesses to develop, market, and maintain Internet offerings. Such disclosure shall be made via a publicly available, easily accessible website or through transmittal to the Commission.
FCC2017-215. Under the rule, all of the practices banned by the 2015 order as well as other practices must be disclosed.:
- Blocking. Any practice (other than reasonable network management elsewhere disclosed) that blocks or otherwise prevents end user access to lawful content, applications, service, or non-harmful devices, including a description of what is blocked.
- Throttling. Any practice (other than reasonable network management elsewhere disclosed) that degrades or impairs access to lawful Internet traffic on the basis of content, application, service, user, or use of a non-harmful device, including a description of what is throttled.
- Affiliated Prioritization. Any practice that directly or indirectly favors some traffic over other traffic, including through use of techniques such as traffic shaping, prioritization, or resource reservation, to benefit an affiliate, including identification of the affiliate.
- Paid Prioritization. Any practice that directly or indirectly favors some traffic over other traffic, including through use of techniques such as traffic shaping, prioritization, or resource reservation, in exchange for consideration, monetary or otherwise.
- Congestion Management. Descriptions of congestion management practices, if any. These descriptions should include the types of traffic subject to the practices; the purposes served by the practices; the practices’ effects on end users’ experience; criteria used in practices, such as indicators of congestion that trigger a practice, including any usage limits triggering the practice, and the typical frequency of congestion; usage limits and the consequences of exceeding them; and references to engineering standards, where appropriate.
- Application-Specific Behavior. Whether and why the ISP blocks or rate-controls specific protocols or protocol ports, modifies protocol fields in ways not prescribed by the protocol standard, or otherwise inhibits or favors certain applications or classes of applications.
- Device Attachment Rules. Any restrictions on the types of devices and any approval procedures for devices to connect to the network.
- Security. Any practices used to ensure end-user security or security of the network, including types of triggering conditions that cause a mechanism to be invoked (but excluding information that could reasonably be used to circumvent network security).
FCC2017-220. It is worth noting that the 2017 opinion does not retain some of the ongoing technical disclosures added by the 2015 opinion, deeming them burdensome. In this respect, it may be foregoing information necessary for enforcement of the other disclosures. FCC2017-225.
Like the Obama FCC, the Trump FCC concludes that its position preempts contrary state and local regulatory positions.
We conclude that regulation of broadband Internet access service should be governed principally by a uniform set of federal regulations, rather than by a patchwork that includes separate state and local requirements. Our order today establishes a calibrated federal regulatory regime based on the pro-competitive, deregulatory goals of the 1996 Act. Allowing state and local governments to adopt their own separate requirements, which could impose far greater burdens than the federal regulatory regime, could significantly disrupt the balance we strike here. Federal courts have uniformly held that an affirmative federal policy of deregulation is entitled to the same preemptive effect as a federal policy of regulation. In addition, allowing state or local regulation of broadband Internet access service could impair the provision of such service by requiring each ISP to comply with a patchwork of separate and potentially conflicting requirements across all of the different jurisdictions in which it operates. Just as the Title II Order promised to “exercise our preemption authority to preclude states from imposing regulations on broadband service that are inconsistent” with the federal regulatory scheme, we conclude that we should exercise our authority to preempt any state or local requirements that are inconsistent with the federal deregulatory approach we adopt today.
We therefore preempt any state or local measures that would effectively impose rules or requirements that we have repealed or decided to refrain from imposing in this order or that would impose more stringent requirements for any aspect of broadband service that we address in this order. Among other things, we thereby preempt any so-called “economic” or “public utility-type” regulations, including common-carriage requirements akin to those found in Title II of the Act and its implementing rules, as well as other rules or requirements that we repeal or refrain from imposing today because they could pose an obstacle to or place an undue burden on the provision of broadband Internet access service and conflict with the deregulatory approach we adopt today.
Summary of the FCC’s change in position
Here’s where I may break the 4th rule of this conversation and oversimplify, but I’m reaching for a fair summary of the change in position.
The 2017 decision removes the 2015 protection for content neutrality, sending chills down the spine of all of us who care about civil liberties and want to hear many voices However, the practical change may be modest. The Obama FCC offered a specific neutrality rule which sounded great to first amendment enthusiasts like me. The Trump FCC purports to achieve the same protection relying on more general consumer protection principles under FTC jurisdiction: Broadband providers offer internet service and that means access to the whole internet; discriminating would be a consumer protection violation. Either way, there is the possibility of an enforcement response.
Enforcement aside, there are fundamental commercial reasons why broadband providers won’t want to dabble in stifling particular political voices. While some broadband providers are affiliated with video entertainment companies, they all know that as to most types of content, they just cannot compete with the raw internet. All consumers want access to the raw internet and broadband providers have no general incentive to block or filter the raw internet.
Most of the historically identified cases of alleged blocking or throttling have to do with commercial disputes, not content censorship. The ACLU is able to cite only two historical instances of arguable political censorship by broadband providers in the United States (none in the last ten years). Neither case involved filtering of content from the general internet. One case involved ATT’s arguable censorship of a concert that ATT sponsored. The other, more disturbing case, involved involved Verizon’s limitation of NARAL’s political use of a text messaging destination. In both cases, the companies swiftly reversed themselves after public embarrassment.
The commercial disputes, as opposed to the political disputes, are typically hard cases with decent arguments on both side of them. Even the 2015 FCC declined to set rules governing the disputes between video providers and broadband providers.
It is hard to judge the commercial power of broadband providers. 2017 FCC made a more quantitative effort to evaluate their power than the 2015 FCC did. The 2017 FCC made a decent argument that, in most markets, there will be vigorous competition: Most markets have at least two providers and two providers may be enough to drive heavy broadband competition because the costs of adding additional consumers are low compared to the initial investment. Certainly, both Comcast and Verizon are advertising heavily in Massachusetts communities where both providers are present.
Without expressing a conclusion as to the local or national market power of broadband providers, it does seem clear that the quantitative questions that the 2017 FCC is asking are important. Just by framing those questions, the 2017 opinion makes a good argument that the FTC, with historical responsibility for market analysis in anti-trust enforcement, will be a more competent regulator. That is hardly obvious given the FCC’s expertise in telecommunications, but, it does make some sense — the kinds of issues that are being decided are business and market power issues, the kinds of issues that the FTC has expertise in, not so much technical issues as to which the FCC may have more expertise.
Arguably, the Obama FCC acted out of largely theoretical civil libertarian fears and made a decision that ducked the toughest commercial issues. The Trump FCC reversed the earlier opinion with a similar passion for the freedom of the market, making classical arguments against over-regulation based on a record that will be most compelling to those already convinced of the dangers of regulation.
Both administrations make strong arguments against state-level regulation of the internet. One state public policy priority does become very clear from this conversation — expansion of broadband competition in all communities.
Resources
The best resources on net neutrality are the competing statements of the FCC (and the incredibly rich commentary on those statements). Additional resources include:
- A Brief History of Internet Regulation, Progressive Policy Institute.
- The Tangled Web of Net Neutrality and Regulation, Harvard Business Review.
- Net Neutrality Violations: A Brief History, Free Press.
- The FCC’s War on the Internet Targets Facebook, Forbes (2015)
- Network Neutrality, Broadband Discrimination, Journal of Telecommunications and High Technology Law
- Net Neutrality Topic Index, the Economist
- What you need to know about the FCC’s 2015 net neutrality regulation, CNET
- Who owns the Internet? Medium
- Economics of the Internet Backbone (2005)
- Electronic Frontier Foundation on Net Neutrality.
- ACLU on Net Neutrality
- Wired on Net Neutrality

Hi Will,
Thank you for taking the time to go through and explain these issues. Here are my thoughts on the issue.
I agree that the differences between the two orders comes down to a proactive vs. reactive regulatory approach. I am personally in favor of a proactive approach as it is easier for the FCC to make rules and implement them, than it is for the FTC to pursue and anti-trust violation. It took a little more than a year for the full FCC rules process to go from start to finish in both cases, and it is difficult for this process to be slowed down. However, an anti-trust suit or similar court case can be slowed down to take several years to run its course. As an extreme example, it took 8 years to break up the Bell system. Since they can continue their anti-competitive behaviors while the case is ongoing, an ISP can continue to illegally make money for years after an FCC rule would have prohibited the practice.
My second comment is about the competition table provided in the 2017 guidance ruling. In context it seems to say that many people have choices for high speed internet, but there are two glaring flaws in this data. First, the speeds reported are the “Maximum Advertised Speeds” (pg 57 of The FCC Internet Access Services as of 12/31/2016). These speeds are often much higher than the actual speeds received. As an example, I pay for up to 60 Mbps, but rarely do I ever see speeds of 8 Mbps (13%) when I use the internet. So while there may be two ISPs who advertise speeds of at least 3Mbps, that doesn’t mean that those speeds are actually being delivered. So I am skeptical of any claims that the market has enough competition to prevent anti-competitive behaviors as stated in the 2017 guidance. In particular, if there is little competition all the notifications about blocking, prioritization, etc are useless, as a consumer would have no way of changing , providers.
My last comment is about the costs of infrastructure. To bluntly put it, the ISPs seem to be purposely avoiding spending their money on increasing their network capacity. Using Comcast as an example, their 2017 financials show $8 billion in cable capital expenditures (they don’t break out expenditures by internet, voice, etc), a $400 million increase over 2016. In the same time frame, they spent $ 5 billion in share buybacks and have authorized up to $7 billion for the next fiscal year. When an ISP is spending the equivalent of 60% of its capital expenditures pumping up its short term stock price, I can’t help but land on the side of Level 3. It seems clear to me that ISPs are pursing a short term profit maximizing strategy (and to be fair, a corporation’s goal is to make profit) at the expense of longer term infrastructure planning and development to the determent of society. It is the government’s job to balance the profit seeking of an ISP with the needs of the people, and ultimately the proactive approach of the FCC is better for this goal than the reactive approach of the FTC.
A question I do have: does the Supreme Court’s recent ruling on sports gambling (i.e. prohibiting state regulation without providing federal regulation) affect the FCC vacating its authority to regulate ISPs?
Sam, great comments.
On FTC v FCC, the basic principle that you have to provide what you tell you are going to provide is already in place for the FTC. In a sense, the FTC is more reactive, but in practice, as far as I know, all broadband providers make consumer representations that imply they will provide internet service, filtered only perhaps for security. I’d be interested to know about reservations in fine print, but fine print reservations won’t necessarily get them off the hook. The FTC can likely enforce their general public representations.
And on the commercial disputes, even the 2015 FCC took a reactive position. The disputes are just too complicated to referee in advance.
Interesting points about the investment levels of Comcast. I don’t doubt that they are playing hardball in some cases.
Also an interesting point about the sports gambling ruling. I don’t know, but I’d appreciate in any light that people can shed on that.
The only thing I would add here is that in business innovation, winning a reactive ruling in your favor has zero value. If I’m out of business, an FTC ruling in my favor is meaningless.
In this hyper competitive market, we must have a proactive ruleset which protects startups, small business and anyone else innovating on the internet.
Seriously, if we don’t get this right – our economy will never be the same. We have only a few major strengths left. One of those is our technical innovation. Ask anyone who has ever started a company with any internet use. If the internet failed them in even the smallest way, that business would be done.
If I came to your site and it took 30 seconds to load and 30 seconds for me to post, I might not ever come back……..
Thanks for a superb summary of the key issues.
You quote Ajit Pai as follows: “The Internet thrived for decades under the light-touch regulatory regime in place before the Title II Order, as ISPs built networks and edge services were born.”
Jon Brodkin in Ars Technica had a response to that concept, one worth reading, including:
“To make today’s Internet service market look more like it did in the era about which Pai fondly reminisces, the FCC could impose line-sharing requirements on copper and fiber phone lines and the cable networks that now dominate the broadband market. Instead, Pai has proposed eliminating net neutrality rules and eliminating the Title II classification that could make such line sharing possible.
“Yesterday, we contacted the FCC’s press office to ask if Pai believes the line-sharing requirements from the Clinton era helped create the large amount of ISP competition that Americans enjoyed in those years. And since Pai believes 1990s-era regulation was a smashing success, we asked if the FCC will consider a return to line-sharing requirements. We haven’t gotten a response yet.”
https://arstechnica.com/tech-policy/2017/05/ajit-pai-accidentally-supports-utility-rules-and-open-access-networks/
Your rules for this conversation, Senator, made me think of Justice Scalia’s highly cogent dissent in the Brand X case related to whether cable-modem-service-providers provide a “telecommunications service”… excellent use of analogies to elucidate the subject matter: car dealers, pizza delivery, puppy dog sales one after the other. And lest anyone’s gut response starts to kick in, Souter and Ginsburg joined him in the analogy-replete Part I.
https://www.law.cornell.edu/supct/pdf/04-277P.ZD
Thank you, Steve, Brodkin makes a helpful point. Here’s a question it provokes: Could the Federal Trade Commission could make that order to unbundle and give ISPs access to broadband lines on antitrust grounds? It’s not clear that miniISPs running on top of broadband would add much consumer value, but it is an interesting thought.
Senator Brownsberger: “Could the Federal Trade Commission make that order to unbundle and give ISPs access to broadband lines on antitrust grounds?”
A chap more knowledgeable than I am tells me:
“FTC does not have rulemaking power. They could not order service or facilities unbundling as a general rule. The only way to secure would be on company by company basis as some sort of remediation for perceived abuses within the FTC’s enforcement powers. Perhaps under their ‘antitrust’ authority, or (and it would be a stretch) for some consumer abuses. Not hopeful this would ever happen.
“Regulation based open access or a divestiture creating a wires company will more than likely only come as a result of FCC epiphany (returning to Computer Inquiry, or reinstating a bunch of UNEs, including fiber-based services) or legislation.”
Senator Brownsberger: “It’s not clear that miniISPs running on top of broadband would add much consumer value, but it is an interesting thought.”
Unbundled network elements (UNEs) were required to be made available at “just and reasonable” rates. So one would anticipate that those miniISPs could constitute a strong check against price gouging as well as against telcos and cablecos deviating from net neutrality principles in ways that harm customers. If a region has just a single telco and cableco competing, I’d think it would potentially be to their great economic advantage to each favor delivery its own content if that is permitted… and if there are no miniISPs able to use the physical networks to offer a competing, more comprehensive, service.
Hi Will,
I really appreciate the amount of research and thought you have put into this. You have added a lot of nuance, but in the end I still feel strongly that the 2015 FCC regulations were superior to the 2017 changes. I have never lived anywhere in the US where I have had a real choice of broadband providers. Sometimes there was a second option, but it was often less than a 10th of the speed of the fastest option. Once there is a dominant provider in an area, other providers have little incentive to upgrade their offerings because they would bear all of the fixed costs of upgrading and capture none of the monopoly rents.
Given that most consumers experience a monopoly, I would far rather have the regulations of what comes through my internet connection be federal than up to the whims of a private company, even if the federal regulations are a bit too much. The FCC is at least nominally accountable to the public, private companies are not.
I am not actually worried about Netflix and Youtube; they are already well established and they can afford to pay the charges, and in any case ISPs know they will not sell many connections if they block them. My concern is for newer less established services that may not be able to pay the fees or may not have the market appeal to force ISPs to carry them. It would have been hard for youtube to ever become what it is today if ISPs could have extorted huge fees for delivering its content back when it first started out. I’m also concerned about what new ideas we will miss out on if ISPs get to decide what traffic makes it through.
I am less concerned about blocking outright, but very concerned about throttling or simply slowing down traffic. Amazon and google have both said that relatively small changes in latency drastically affect their traffic and sales numbers. Even slightly slowing down a new social network (for example) could make it completely impossible for it to compete with existing services.
Finally, I wanted to address the notion that net neutrality would require lighter internet users to subsidize video streaming services. This is perhaps true in theory, but in practice I doubt it is a very meaningful claim. There are already tiers of service (different speeds) and my experience is that my friends that use more streaming services pay more for the faster connections. In fact, I think if it weren’t for streaming video, wired broadband might have already been superseded by mobile broadband, which is already fast enough and cheap enough for almost all web use *except* video streaming. The notion that services like Netflix are dumping data into ISP’s networks is fallacious. Broadband *users* are *pulling* the data in because they want it, and they have already paid for that service.
Thank so much for weighing in.
I don’t think it is clear that “most consumers experience a monopoly”. The data table excerpted in the post above is arguably to the contrary. But, I agree that there is a reason at least to have a concern about limited competition in many markets. The FCC in 2017 is not saying that Broadband not be regulated. They are saying that the market judgments are better made by the FTC than the FCC.
I think you are right to raise concerns about the barriers for new commercial entrants, but it may be that new entrants have good options for purchasing access to content delivery networks that may have relationships with ISPs. They don’t need to build a CDN of their own until they get big and then they will want to. Right or wrong, that’s a judgment that requires market analysis of the type that the FTC does routinely.
Good point well taken that the tiering of speed options sorts out the consumers and reduces cross-subsidization. Also agreed that consumers are asking for Netflix — it isn’t sending anything that isn’t asked.
Hi Will,
I applaud your thoroughness in this analysis. I have a few comments which I will post below, but I would like to specifically draw your attention to your use of the term CDN and what a CDN does. I reply here because you use that term in your reply.
“but it may be that new entrants have good options for purchasing access to content delivery networks that may have relationships with ISPs.”
NO. This is not what a CDN can do. This is important.
A CDN does reduce the number of jumps a request has to make to get the data it is requesting. However, a CDN cannot exist without all of the other network principle’s being in place and does not, in any way, sit outside of the existing communication channels.
A CDN is just a collection of cached data placed in geographically disbursed locations to reach users faster. That’s it. You cannot get around an ISP or backbone by using a CDN – it’s just closer to the end user, but still on the same networks.
If a new entrant to a market is being hindered, using a CDN will do nothing to help them.
I do understand what a CDN is.
But, to the extent that the CDN already has interconnection agreements with major ISPs, then the entrant will get the benefit of those. Some CDN’s are doing that; some are not.
Clearly, in the case of the CDN I use, Cloudflare, packets have to make several hops on the backbone to get there as the traceroute above in the post shows. So it is not delivering directly to Verizon.
But Google’s CDN, for example, appears to deliver straight right into Verizon. Take a look at this traceroute from my home computer to google.com:
Hop 6 is still within my broadband vendor, Verizon — Alternet was acquired by Verizon and appears to be in NYC. Hop 7 is in Mountain view!
Hi Will. Thanks for the reply. Your level of engagement on this is impressive and should be a model for others.
Alright, long comment below, but here is the summary: the issue is that Verizon still delivers the data to you from Google. So, if you were a new entrant into a competitive market, using a CDN does not get you around the Verizons and Comcasts.
CDNs are complicated and tend to incorrectly further complicate the ‘Net Neutrality’ discussion – but my point is that they should not be seen as a complication in the discussion. If the question is ‘Under the FCC 2017 rule, can ISPs interfere with network traffic through their network to the consumer’. The answer is yes, regardless of CDN usage.
But, your example also has some important flaws I want to point out simply because you do have an understanding of CDNs (and networking), but I think you are missing some key points …..
You are correct that Google has a ‘peering’ agreement with Verizon (and Comcast) to bypass the backbone. You are also correct that Google has an agreement to host CACHED data within the Verizon network.
However, how does a user get to your data? Your traceroute example to google.com is unintentionally misleading – although your statements about it are correct. It’s misleading because routing to google.com is asking for no CACHED data – so it gets routed to Mountain View. Google.com is a blank slate used to lead to other sites (obviously).
I think a better example of a CDN traceroute would be to use your website again as you did in your original post.
I know you know this stuff, but keep this in mind while thinking about my comments: CDNs only host CACHED data (data already stale. This data van be proactively placed there by the CDN or requested by a user and then put there by the CDN. either way, it’s cached data and not LIVE).
Why does it matter that a CDN is cached data? Well, for one, it helps get a sites ‘static’ files to the user faster. Files which do not change often, such as images, javascript files, style sheets and other files like this that usually take users a while to download.
cloudflare as a service does more than provide a CDN, but let’s just stick with the CDN model if that’s OK.
What your CDN does not CACHE is what really matters – your post, these comments and following comments. They are ‘dynamic’ (always changing) and are not good matches for caching.
So, when I make a network request to https://willbrownsberger.com/understanding-net-neutrality/ 90% of the page which is returned is made up of cached images and static files like .js and .css.
But this cached material is meaningless without the text of this post – which in your case comes directly from the server hosting your domain and then fed through Cloudflare. If it didn’t, I would not get your next comment because the page would be cached.
And, even if that hosting server is on the Verizon network and maybe a CDN figures out how to do dynamic caching (they have), the issue is that Verizon still delivers the data to me from your site.
Great points. I guess I’m focused on video. Most of the high cost video material is static and can and should be forward based.
There are serious holes in all of these analyses — and it starts with some essentials that have been removed from the discussion.
And the issues are much larger than the net neutrality framing.
1) First and foremost, Verizon’s entire FTTP networks for FiOS are Title II today — and have been since the Belmont franchise was signed, and updated.
http://www.belmont-ma.gov/sites/belmontma/files/uploads/verizon_cable_television_renewal_license_7-31-17.pdf
“The parties recognize that the FTTP Network is constructed, operating and maintained as an upgrade to and /or an extension of the Licensee’s existing Telecommunications Facilities under Title II…”
And this was done so that the expenses would be dumped into the state utility, Verizon MA, and that these wires could also be used to illegally build out the wireless networks for Verizon Wireless—instead of upgrading the State.
So, just to start, this directly contradicts the FCC’s decision on Net neutrality — as Title II is the investment mechanism.
And this also shows that the companies have already prioritized– not even illegally, to give financial advantages to its own subsidiaries–harming all competition, but also giving these companies data, marketing info, price advantages, cross-subsidies on all expenses, the rights of way — a long litany of advantages this is only the surface issues.
We wrote an entire report with documentation on issues that should be investigated.
https://ecfsapi.fcc.gov/file/1041707743056/VerizonMAreportjan17.pdf
Let me be specific to Massachusetts.
1) The state was supposed to be upgraded with fiber optics, starting in 1995 when state laws were changed to give now Verizon more money to put in 330,000 fiber optic lines. -We filed a complaint about this in 1999
http://newnetworks.com/wp-content/uploads/Masscomplaintfinal1999.pdf
2) This work was never done but built into all local rates were increases and excess profits to pay for these fiber optic networks.
This was not FiOS, which was announced in 2004.
3) Verizon was able to put the FiOS FTTP wires in as “Title II”, and even the current FiOS deployment in Boston is Title II — and I assume Belmont.
4) This was done so that the expenses could be dumped into the local service category.
5) Verizon in all states, decided to take the construction and divert it to build out –cross-subsidize the wireless networks
6) Fixing Net Neutrality, then– the companies are already giving their own affiliate companies, like Verizon Wireless or Verizon Online, massive financial investments that should have been going to properly upgrade the networks.
7) These networks should never have been closed to competition and the FCC’s other proceedings, from shutting off the copper networks, preempting state and federal laws, blocking competitors from using the networks, privatizing the state utility networks and even making claims about 5G wireless, (which are just a con to get rid of the rest of the regulations) — are much more critical.
8) At this time, Verizon has stopped selling or even maintaining the existing networks and MA has not made any attempts to call for investigations and audits of the cross-subsidies or other important points.
If Verizon Fiber Optic networks are Title II, and customers have been funding these networks, then every aspect of the FCC’s decision could be challenged based on these facts. — No state or even city has done that.
And Boston? Verizon, with the help of the Mayor, lied to the public about the deployment.
?It is not spending $300 million as part of the current build was put in 2005
?It is not doing fiber to the home but is cross subsidizing the wires to the cell sites, which will be done as ‘FiOS’ as a wireless service’.
?It took billions of dollars to do the Verizon Wireless networks instead of properly upgrading and maintaining the state.
?And all of the financials have been seriously cooked; there have been no audits of the books for over a decade
?The FCC’s cost accounting rules now dump the majority of expenses into the local service – so that the copper networks appear unprofitable, and the company can show losses and make claims it can’t afford rural areas—even though the company collected thousands of dollars per home to do this work since the 1990’s.
The FCC’s rules were ‘forborne’, (on the books but not enforced) but it is the basis of how the expenses are allocated to the different lines of business– and the financials from Verizon MA and NY show they are still in use.
Finally, this is all about infrastructure. Customers have choice about whether to be on Facebook or have Netflix — Verizon, for example, controls the telecom infrastructure, which is also for wireless, has a deal to bundle their wireless service with the cable companies – and the reason there is no serious competition is because — VERIZON NEVER SHOWED UP TO BRING IT. Instead, there is a defacto agreement with the cable TV companies to split up the markets and services– for critical infrastructure and wireless. Verizon MA controls 99% of the incumbent telecom infrastructure — which they failed to properly upgrade and maintain and are now handing it over the state utility (FiOS’ FTTP is part of the utility infrastructure) to the Wireless company– as private property…
Feel free to contact us about what should happen in MA next, and at the FCC.
Bruce, thank you. Honored to have a knowledgeable professional with a national reputation weighing in here.
You are raising some important larger issues.
Good morning Senator. Thank you for taking a break from your beloved Internet to march in the Memorial Day parade yesterday along with Rep Rogers and ? Rep Hecht. It was inspiring and uplifting to see you with other town representatives. I regret not having prepared earlier and appearing with pompoms for all of you. Godspeed.
Thank you for your support, always!
Good morning,
This is a really fantastic and well-researched piece about Net Neutrality, and I am glad to see that you’re taking the issue seriously for both sides. I am in favor of Net Neutrality, but can appreciate a civil discourse.
For me, the big concern is throttling when I don’t have any other options. I was told when I moved into my current apartment that Comcast was the only provider that serviced this building. Given Comcast’s reputation for customer service and repairs (to be clear, I mean their pretty bad reputation), I would be more comfortable with the 2015 protections than simply putting my faith in Comcast to do the right thing.
I have also got friends who create and host podcasts, which Net Neutrality could also impact. While I don’t know how much internet traffic goes to podcasting, I know that they are growing in popularity. For more independent teams, any option that requires paying to maintain their connection to the fanbase could be the death knell of those creative projects. For one of these projects in particular, it is a source of income for the creators and a source of joy and acceptance for the fans.
As with my situation, I know public pressure is a force, but I still don’t have a lot of faith in the ISPs to keep their networks neutral. I fear that it will be “a death by a thousand cuts” scenario, rather than an instant change in costs.
Thanks for your time and attention,
Grahame Turner (Brighton)
Thank you for this helpful overview.
When it comes to biasing some content over others, I don’t think the issue is that some content would be blocked, but that sites could be made slower or faster — which is a way of pushing people toward some websites and away others. The ability of ISPs to privilege some content over others reinforces the market power of the big players already in the market. We’ve seen in recent years that Facebook and Google are not good actors, and we’ve been seeing a growing awareness of the negative impacts of private monopolies. This stymies innovation (who knows if a site that accomplishes their function better will come along in the future?). Moreover, ISPs could seek to discriminate against Internet-based services that provide services that compete with what the ISP’s company also provides (e.g., phone services video services).
.
Definitely the real issue, but this is as appropriately an FTC issue as an FCC issue. And note that the Obama FCC did not tackle this with their rules. They recognized it is too complicated to write prospective rules about.
I believe that the former net neutrality rule, the one that the current FCC is overturning is about power. The big Cable companies, and ISP’s in general have not up to now tried to exercise their ability to shape what we the people see on the net. But I believe that had more to do with technical ability than the desire to squeeze more money from whom ever would be willing to pay them. The rule was forward looking, because it prevented a problem from happening before it became a problem. I remain totally concerned that if an ISP is not required to provide equal access, payola will result in some shape or form. I view paid prioritization as invitation to ISP’s to put their favored search, content, and anything else before neutral results. It will be big brother by information monopoly. ISP’s and their suppliers now have the ability intercept and change what one sees from edge players.
By the same token,Comcast plays with developers (Avalon comes to mind) to get exclusive rights to sell to tenants in large developments in exchange for build outs and payments. These arrangements prevent competition to competitive supply of internet services in large and small parts of the housing stock. It also happened to me in the building I am in now, that I could not get RCN service because the landlord has an arrangement, and wants payola to let in a new service to his building. So I pay more for less. So if they are willing in one significant way to limit choice why should we trust them to not limit choice in others. They say they will not now, but now they want something. Later is later and you, the public, the legislature will not be looking so hard later.
In my opinion it is laudable that you are trying to come to grips with this issue. But I think that you are taking a lawyer’s approach which concentrates on specific issues and solving the specific problems and looks at specific consequences of a policy decision that are being presented to you. I would much rather take a holistic framework approach that says these are the principles we want imposed. The specifics of a particular outcome are not that important. The principal is what is important. If netflix or Utube is overloading a network, the solution is to add capacity, and competition. Monopoly firms however find more profit from charging more for existing capacity and blocking competition in big and small ways. They have smart people who know this and actively undermine threats to profits.
It is the difference between the approach of the GDPR and what we have for hodge-podge of privacy rights in the USA. The GDPR in the EU covers everything about privacy rights. There are no exceptions. It is a universal rule. In the USA, we have rules for banking, and health care and some kinds of government info gathering, kind of. But no or little rules elsewhere. And in US law, there is not actual privacy right, it is totally implied , by contract and by legal decision not really by law. Congress and the executive have not passed a law that says here are your privacy rights and responsibilities. So privacy is a mutable legal concept that get interpreted and twisted in time. My concern is that with net neutrality loosely defined, if we do not establish the frame work and principals for access. We will forever be chasing the goal and the rich smart and powerful ISP’s will always have a way to frankly purchase influence of decision makers to protect their monopoly profits.
“The big Cable companies, and ISP’s in general have not up to now tried to exercise their ability to shape what we the people see on the net. But I believe that had more to do with technical ability than the desire to squeeze more money from whom ever would be willing to pay them. The rule was forward looking, because it prevented a problem from happening before it became a problem.”
I couldn’t agree more.
Thanks, Dan.
I might agree with you on the privacy issue — much bigger in my mind than the net neutrality issue and very distinct.
As to prioritizing content for money, the real issue is google and facebook and that is precisely their business model!
I echo Stephen Ronan’s compliment.
What this second white paper of yours doesn’t touch is what your pointed to in the first: the quality of the content being both selected and transmitted by Google, Facebook and the like.
So while the mechanics of transmission and how to regulate them is being explored in great detail, the arguably more important qualitative aspects of the internet are allowed to seep into the sands of indecision and uncertainty.
I hope you will not let that happen while you’re dealing with the complex issue of net neutrality. As I tried to point out in my comment to your first post, while pipe size is easier to deal with because it permits quantification to a certain degree, monitoring and controlling the quality of content should not be left in the hands either of government or of the content providers. What is needed is the development of an internet fourth estate, a free press that focuses on the quality of the content being funnelled to the consumers.
Legislation cannot make this mandatory, but could certainly create a fertile breeding ground atmosphere for acting as public defenders in the best sense of that term. And while this is clearly already happening (the likes of CLF, ACLU, UCS, NRDC, Sierra Club, etc. come to mind), much more is needed to tilt the balance of content from mush (or worse) to healthy nourishment.
Agreed — need to focus on the content providers. Separate issue and I’ll come back to it.
Enough from me. I didn’t see this in your sources (I might have missed it).
From the people who built the internet on why the FCC has it wrong. There is not way I could say it better:
https://ecfsapi.fcc.gov/file/1071761547058/Dkt.%2017-108%20Joint%20Comments%20of%20Internet%20Engineers%2C%20Pioneers%2C%20and%20Technologists%202017.07.17.pdf
Will
Really appreciate your open thought process of this complicated issue. I am wondering if you are trying to resolve your position on the Obama versus Trump administrations positon or is there reason you believe the MA legislature has a role to play.
I think the internet is not a public utility in as much as as internet last mile service is not a monopoly, in face there is competition between wired providers as well as wired versus wirless providers. This competition fuels innovation.
Furthermore cities and town can provide more competition by opening up to more providers. I hope you will think becfore regulating as monopoly utilities are among our least innovative and worse performing industries-think National Grid and MBTA.
You write, “The 2017 decision removes the 2015 protection for content neutrality, sending chills down the spine of all of us who care about civil liberties and want to hear many voices However, the practical change may be modest. The Obama FCC offered a specific neutrality rule which sounded great to first amendment enthusiasts like me. The Trump FCC purports to achieve the same protection relying on more general consumer protection principles under FTC jurisdiction: Broadband providers offer internet service and that means access to the whole internet; discriminating would be a consumer protection violation. Either way, there is the possibility of an enforcement response.”
It is interesting to listen to civil liberatarians discuss net -neutrality on one hand worrying about content neutraliy yet in light of Facebook’s (in)action in the 2016 presdidential election these same folks want social media companies to filter content, some might call that private industry censorship?
Again if you are worried about providers “stifling particular voices” why not trust the internet user communities to keep feedom of expression flowing.
As I look at the net-neutrality issue in general, I believe the 2015 Obama FCC ruling was an action in search of a problem that did not exist. Based on the run up to the ruling. there was active lobbying by broadband providers and content providers and it seems as the 2015 ruling gave the nod to the later. But did it really do any good?
Perhaps MA should wait a while and let markets give their verdict based on the action of citizens in their private independent decisions. Let broadband and content providers innovate and battle, keep government out of the fray until we see real harm. This is not a matter like smoking, clean water or any of the myriad of issues that got government regulation because their was a real problem needing government help.
I like the Rules for the Conversation a lot, especially “Let’s not reason based on political affiliation”.
I do not understand this post at all. I bet most of your audience does not understand. I think you should ask a few IT engineers. I may know a few.
Appreciate the tons of info, but no way a regular person like myself can slog through it, much less weigh the options. The original issue I heard of was: preferential speeds/treatment for subscribers who pay a LOT more. I get my internet through my cable TV provider — it is already half of my monthly bill, well over $1000 per year. I don’t want to be at the back of the information supply line just because I’m a single user, not a company.
Senator, you deserve the world’s record for quickly tackling and absorbing a challenging set of thorny issues that almost no one wants to face.
I look forward to your continued progress on this.
I have only one correction:
A network is not a “collection of linked devices” (your words from concept #2).
A network is only the cables and servers that sit between all the customer devices (computers, tablets, phones, etc.). The devices belong to the customers, whereas the networks belong to the providers. Customer devices connect to and use provider networks, but only while both sides agree; eventually, many customers go elsewhere.
Dear Will:
Thank you for the detailed and diligent approach to this issue and the for the nuance and balance which provide the framework of your report. I read most of it, and even though I think of myself as a techie nerd, my eyes did glaze over in parts.
I think you re-enforced my original view: people who use more bandwidth should pay for it. If content providers offer better content, people will pay more for that too. If network infrastructure providers have increased revenues from better services, they will innovate more to the benefit of all.
The invention of the cell phone was instrumental in breaking down the old telephone monopolies. The advent of VOIP has done wonders to lower telephony costs by circumventing the old boundaries of land-line telephony.
Without the innovation we have had from a free-market internet, we would not have the plethora of voice and video services we have today. In your lexicon, I support the “Trump FCC”.
Thank you for your amazing work.
Charlie
Will: You’re coming to a conclusion that I dislike, but I don’t have confidence is wrong :-}. I do want to call out that your conclusion is at least somewhat dependent on the assertion that most broadband markets have at least two competitors in them. That has not been my impression from following this issue for several years (primarily on arstechnica.com, which is a level-headed technology news site I trust), and the only support you give for it is the FCC justification for the repeal of net neutrality, which is a source I do *not* trust. And naively, if many people have no internet access (== zero providers) available to them, doesn’t that suggest an intermediate space where many have only one?
I would suggest that, before setting Massachusetts policy on this issue, you get an independent evaluation of the prevalence of broadband competition in this state.
Double disclaimer: a) I work for a large internet edge provider (Google) as a networking engineer, and b) this comment represents my opinion only and has nothing to do with the position of my employer.
Thank you for this suggestion. Very well taken. I’ve tasked staff to see if we can dig out a current Massachusetts specific study on BIAS market shares.
Will–
Like almost everyone on this thread, I’m impressed by the sheer volume of information you’re waded through. However–I’m also troubled by the fact that ultimately you’re only vote in a legislature composed of *much* less savvy representatives. Worse, what is likely to happen if 50 different states each come up with unique Net Neutrality rules? That’s already happened in other industries, and the outcome is guaranteed chaos.
As you’ve mentioned in your post, *both* the Obama and Trump approaches specifically mention that one federal set of rules should apply everywhere in the U.S. I think that’s a sensible position for Massachusetts to take, and I sincerely hope that you’ll end up voting AGAINST any bill that tries to create state-level Internet rules.
If states pass overreaching rules, the certain result will be litigation. The courts will straighten it out. Hard to think of something more interstate in nature than the internet.
In wondering about the scope of state actions that could survive FCC attempts to preempt, I find Harold Feld’s analysis particularly hepful: “Can The States Really Pass Their Own Net Neutrality Laws? Here’s Why I Think Yes.”
http://www.wetmachine.com/tales-of-the-sausage-factory/can-the-states-really-pass-their-own-net-neutrality-laws-heres-why-i-think-yes/
I don’t mind admitting that some of your discussion went over my head. On the other hand, Farhad Manjoo’s column today presents a simpler perspective, and what many of us fear will happen. As he said, it won’t happen tomorrow. But monopolies, or near-monopolies, are not generally good for anyone other than the companies themselves.
https://mobile.nytimes.com/2018/06/11/technology/how-net-neutrality-repeal.html?rref=collection%2Fsectioncollection%2Fbusiness&action=click&contentCollection=business®ion=rank&module=package&version=highlights&contentPlacement=11&pgtype=sectionfront
The implicit point he makes is that most of the power is with the content companies. And the FCC ruling is basically tangential to that.
“Enforcement aside, there are fundamental commercial reasons why broadband providers won’t want to dabble in stifling particular political voices. While some broadband providers are affiliated with video entertainment companies, they all know that as to most types of content, they just cannot compete with the raw internet. All consumers want access to the raw internet and broadband providers have no general incentive to block or filter the raw internet.”
The example of Comcast messing with bittorrent is an important example of past abuse. Ajit Pai is obviously downplaying it but others too I think. Comcast didn’t back off in any great hurry. It took quite a lot to bring it to the public’s attention. And I thought I’d read something to the effect that we didn’t have the laws at the time for anything to happen other than Comcast bowing to public pressure and that the 2015 regulations were supposed to have changed that.
We should have more imagination about what the Internet can become. It should be comprised of network software defined and created by its users — protocols and programs potentially quite different from what we have now. What new programs and protocols are in the works that people don’t know anything about and would not notice if Comcast and Verizon nipped them in the bud? I.e. what’s the bittorrent of today? I think of things like Tor or the Interplanetary File System, but there are probably other things I’ve never heard of and there will be things later people haven’t thought up yet. If ISPs interfered with these how much outcry would there be if they’re squelched before becoming popular? There were principles in the 2015 rules that sounded helpful while, if I’ve not misread, the new rules simply ask that the ISPs disclose frowned upon practices. Okay, more stuff for the fine print no one reads. Big deal.
But I think this is better for Markey to take up (which I guess he is). Massachusetts should concentrate on proactive ways to get more local competition and help rural or impoverished people with their access. The competition should be not only in number but in kind. E.g. I would prefer to get my Internet from my municapility or from a nonprofit with a social mission, not from the likes of Comcast or Verizon. So Massachusetts should make sure the incumbent providers can’t interfere with that happening or other kinds of competition cropping up, and if there are things it can do to help local entities to provide alternatives to the big guys, do that. I miss the dialup days when I’d get my Internet from cute little organizations like TheWorld, thecia, or back in Nova Scotia where I dialed in to Chebucto Community Net to get Internet. There’s no way back to that kind of ISP world?
Thank you, Mike.
I absolutely come to the same bottom line: The state should focus on improving competition!
INTERNET AND MEDIA
[LWVCT Position: Adopted 2008]
A Neutral Internet: “Net Neutrality”
The LWVCT believes that a free and open Internet is increasingly important to the protection of individual liberties – freedom of speech, freedom of the press, and freedom of association – guaranteed by the U.S. Constitution and by the Connecticut Constitution. The League also believes that net neutrality
protections are essential for political discourse, dissemination of news, and democratic participation. Therefore, the League of Women Voters of Connecticut supports the LWVUS position to protect the open, neutral, nondiscriminatory nature of the Internet. To further this position, the LWVCT supports efforts by the State of Connecticut to protect the open, neutral, nondiscriminatory nature of the Internet.
Universal High Speed Internet Access for Connecticut
The League of Women Voters of Connecticut supports making high speed Internet access available to all Connecticut residents, without charge, through schools, libraries, and other secure public buildings. High speed affordable Internet access is an essential service that should be readily available to all Connecticut residents and businesses. State and local government policies should support broadband, wireless, and other means of high speed Internet deployment throughout the state.
Efficient, high speed access to the Internet for all Connecticut residents- regardless of geographic location or neighborhood demographics-is a necessity for assuring equal access to local and state government, for maintaining openness and transparency in government activities, for communicating with legislative leaders, for engaging in political discourse, for competing in the global marketplace, and for assuring that voters receive the information they need to participate in our democracy.
Community Access and Public Affairs TV:
Public, Educational, and Governmental (PEG) TV & the Connecticut Network (CT-N)
The League of Women Voters of Connecticut believes that community access television channels – for public, educational, and governmental programming
– must be adequately protected, promoted, and funded, regardless of the provider of TV/video services to Connecticut residents. Statewide public affairs programming, such as provided by The Connecticut Network (CT-N), must be adequately protected, promoted, and funded by the state legislature and available to all Connecticut residents, regardless of the provider of TV/video services. Government should provide opportunities for citizen participation in decisions regarding community access, or PEG, TV.
Access to the public airwaves through modem TV/video communication is essential to the public interest and to League of Women Voters’ mission and purpose- to protect civil liberties, to ensure open, transparent government, and to promote the public’s right to know. To protect the public interest, high quality PEG transmission and PEG availability on basic service tiers are essential.
Background and Action:
At the 2006 LWVUS Convention, LWVCT proposed and caucused for a resolution to recognize a “Net Neutrality” position as based on League Principles. The Convention delegates adopted the Net Neutrality resolution but rejected another (also introduced by LWVCT) in support of community access television. Meanwhile, the Connecticut Dept. of Public Utility Control (DPUC) ruled that Internet Protocol Television (IPTV), such as AT&T’s U-verse service, is technically different from cable television (CATV) and so should be regulated differently. A federal judge ruled in contradiction to DPUC that IPTV is just like CATV. An appeal was filed.
In 2006-07, while LWVCT studied media issues, the General Assembly passed legislation that established the Connecticut Broadband Internet Coordinating Council (CBICC), consisting of academics, public officials and industry representatives, to study and advise the legislature on ways to increase high speed Internet availability in the state. Another bill, PA 07-253, revised statutes to incorporate IPTV regulation in the public utility statutes; in general it relaxed regulation of the industry This bill also established two special funds, one for capital needs of PEG TV programming and production and another to defray property taxes in municipalities where IPTV is available.
In 2008, the LWVCT concurrence was still in process, but unintended consequences of PA 07-253 had come to light. Delivery of PEG programs by an IPTV service provider was found to be substandard in other states; however, problems were difficult to address in the new regulatory environment. PEG entities collectively tried to push legislation during the 2008 legislative session to correct this, but all proposals failed. The LWVCT monitored legislative initiatives in this area including the bill favored by PEG entities.
In April, 2008, the LWVCT achieved state concurrence on its media study positions on Net Neutrality, universal access to high speed Internet, and community access television. Activity concerning Net Neutrality has taken place in Congress, in federal courts, and in the Federal Communications Commission. Although the LWVUS position is not a national League priority, the LWVCT continues to monitor national events.
During the 2010-2011 biennium, the LWVCT continued to attend CBICC meetings and offer comments. Meetings continued to the end of 2011, months after the Council’s establishing legislation was repealed. Members discussed a state application for a federal grant (BTOP), the Internet needs of public entities (municipalities, state library, CT Education Network) and corporate needs for less regulation
The LWVCT also participated in the Connecticut Academy of Science and Engineering (CASE) Broadband Study Committee. The Committee was tasked with creating guidelines for the development of a strategic plan for accessibility to broadband services in the state. The Committee’s report was issued for the 2012 legislative session; ironically, it is not available on the CASE website. No legislation followed its recommendations.
In 2013, bills were submitted by the telecommunication industry to relax regulation on landline and Voice over Internet Protocol (VoIP) telephone service. In oral testimony, industry representatives argued that this was needed so that they could devote more resources toward wireless broadband infrastructure. The line workers union and AARP opposed this effort, contributing to its defeat.
In the area of community access television, 2009-10 was dominated by budget deficits and our efforts spent in futilely defending a special fund for capital expenses from “sweeps” into the General Fund. These sweeps were executed again in December 2012 and built into the state budgets for FY2014 and FY2015. The popular capital grant program is on hiatus until the fund is replenished. The state budgets also completely drain the fund for municipal tax relief.
During the 2009-2012 legislative sessions, the LWVCT testified and advocated for good signal quality in PEG programming on any cable/video service and for a regulatory performance review of the industry. Although the latter concept was included in a bill that won bipartisan support and passage in the House in 2011, the bill died in the Senate. The LWVCT also testified in favor of a failed bill which provided incentives for satellite TV providers to carry the Connecticut Television Network (CT-N). In 2012, only performance review was proposed, failing again in the Senate. In 2013, no cable/video-related legislation emerged from committee.
In 2011, the Public Utility Regulatory Authority (which replaced DPUC) initiated a docket to consider performance of Community Access Providers (CAPs), entities officially designated to provide PEG access television programming. The LWVCT submitted written comments to the agency on this docket in October 2011, incidentally noting the need to review the industry’s role in PEG programming and the role of broadband Internet in this area. In the procedure following from that docket, only two CAP reviews — for Cox Communications and for Skye Cable XIII in the Waterbury-Comcast area — were begun in 2012 and continue as of this writing. There are over thirty CAPs in Connecticut.
There were two positive funding developments in 2014. The Bonding Bill implementing the Governor’s budget recommendations included $3.23 million for “production and studio equipment” for CT-N, as well as $3.5 million for PEGPETIA. And the budget adjustment bill for FY 15 increased the revenue intercept which funds the operation side of CT-N from $2.5 million to $3.5 million.
In 2015, LWVCT supported funding to explore building a public gigabit network in CT, to make faster internet access available and affordable to consumers. A new Office of Broadband Advocacy was established in the 2015-2017 budget implementer (SB 1502; PA 15-5), adopted in the June special session. Although the “special, nonlapsing” capital equipment fund for PEG TV stations escaped budgetary “sweeps” in the regular session, the account was completely cleaned out in the special session’s revenue bill (HB 7061; PA 15-244.
2017 the League publicized and supported the campaign to defend net neutrality.
Of equal concern to net neutrality and actually under state property law control is the practice of local network providers, like Comcast to offer property owners and managers of larger projects something for blocking out competition in a development. There by establishing a small competition free pool of customers. They then because of no regulation are able to offer non competitive rates to these stuck customers. It may only be 10 units here and 100 units there, but eventually over time they have a serious number of units which tenants have no choice and they are smart enough to manage their billing system to extract monopoly profits from these property developments. This happens in both residential and commercial property. I know it happened to a someone who lives in a development in Waltham.
Dan,
Please contact my office offline and let us know the specific examples that you have in mind and we will investigate.
I agree that this is troubling.